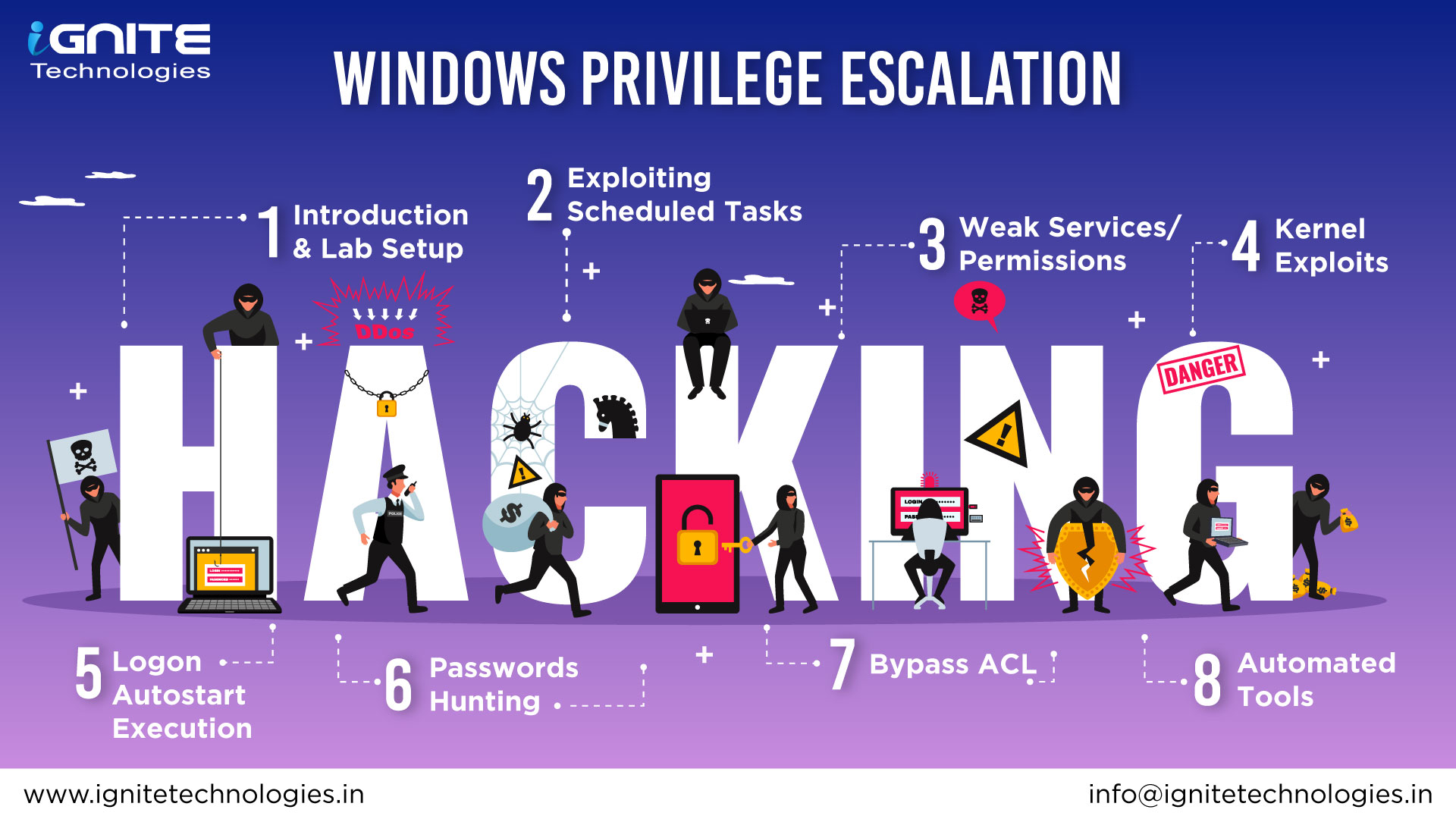
🪟 Windows Privilege Escalation
A practical Windows Privilege Escalation cheat sheet and reference guide designed for penetration testers, red teamers, and cybersecurity learners to understand how attackers escalate privileges on Windows systems during post-exploitation.
🔵 Telegram – Join Channel
⚫ Twitter/X – Follow Us
🟣 Discord – Join Server
💼 LinkedIn – Follow HackingArticles
🚀 Join Our Cybersecurity Training Program
Hands-on training in Penetration Testing, Red Teaming, and Cybersecurity.
| # | Topic | Description | Article |
|---|---|---|---|
| 1 | ⚙️ AlwaysInstallElevated | Abuse MSI installer policy to execute payloads with SYSTEM privileges | Read Article |
| 2 | 💾 SeBackupPrivilege | Abuse backup privileges to read sensitive system files like SAM and NTDS | Read Article |
| 3 | 🌐 DnsAdmins to DomainAdmin | Escalate privileges from DNSAdmins group to Domain Admin | Read Article |
| 4 | 🎭 SeImpersonatePrivilege | Exploit token impersonation privileges for privilege escalation | Read Article |
| 5 | 🧨 HiveNightmare | Exploit vulnerable permissions on registry hives to dump credentials | Read Article |
| 6 | 🔑 Registry Run Keys | Abuse autostart registry keys to gain persistence and escalate privileges | Read Article |
| 7 | 🚀 Startup Folder | Execute malicious programs via Windows startup folder | Read Article |
| 8 | 🔓 Stored Credentials (Runas) | Abuse saved credentials with runas command | Read Article |
| 9 | 🗂️ Weak Registry Permissions | Exploit writable registry keys to escalate privileges | Read Article |
| 10 | 🛠️ Unquoted Service Path | Exploit improperly quoted service paths to execute malicious binaries | Read Article |
| 11 | 🖥️ Insecure GUI Application | Exploit GUI applications running with elevated privileges | Read Article |
| 12 | 🔧 Weak Service Permissions | Abuse misconfigured Windows services for privilege escalation | Read Article |
| 13 | ⏰ Scheduled Task / Job | Exploit scheduled tasks with weak permissions to execute payloads | Read Article |
| 14 | 🧬 Kernel Exploit | Escalate privileges by exploiting vulnerable Windows kernel drivers | Read Article |
| 15 | 🧾 SamAccountSpoofing (CVE-2021-42278) | Exploit Active Directory vulnerability to escalate privileges | Read Article |
| 16 | 🖨️ SpoolFool | Exploit Windows Print Spooler vulnerabilities for privilege escalation | Read Article |
| 17 | 🖨️ PrintNightmare | Exploit Print Spooler vulnerability to gain SYSTEM privileges | Read Article |
| 18 | 🧑💻 Server Operator Group | Abuse Server Operators group privileges to escalate access | Read Article |