The modern internet is built on legacy protocols such as IPv4 and IPv6. While these protocols have scaled globally, they were not designed for:
- Quantum-era security threats
- Decentralized trust models
- Built-in encryption and identity
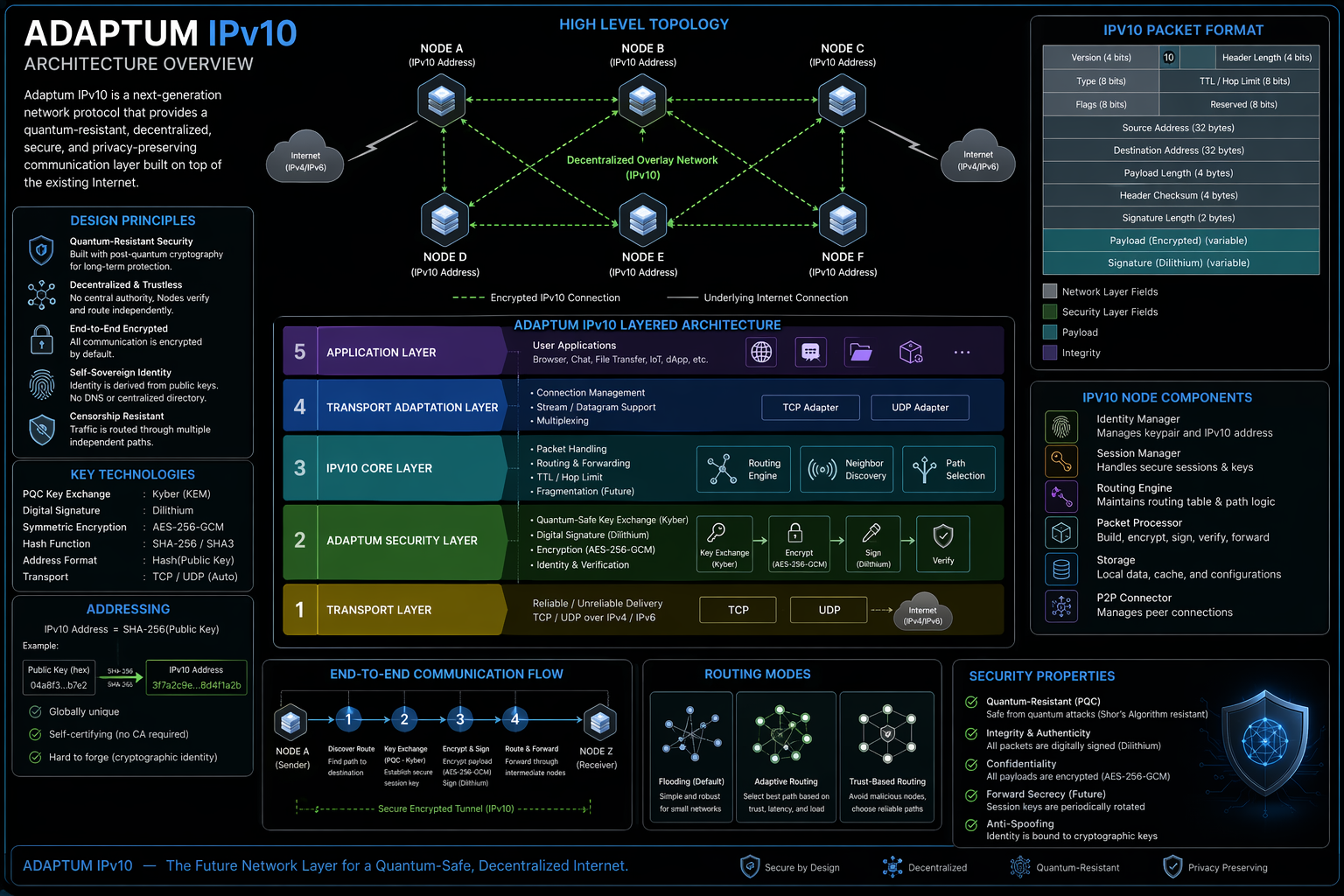
Adaptum IPv10 introduces a new overlay network protocol designed to address these limitations by integrating cryptographic identity, encrypted communication, and decentralized routing.
Adaptum aims to create:
A secure, decentralized, and quantum-resistant network layer that operates independently of centralized control.
All communications are encrypted and signed by default.
No reliance on centralized authorities.
Nodes derive identity directly from cryptographic keys.
Designed to integrate post-quantum cryptography.
Adaptum IPv10 operates as an overlay network on top of existing transport layers.
Application Layer
│
IPv10 Routing Layer
│
Adaptum Security Layer
│
Transport Layer (TCP / UDP)
│
Internet (IPv4 / IPv6)
Each node in the network contains:
- Address (Hash of Public Key)
- Cryptographic Keypair
- Peer Manager
- Routing Engine
- Session Manager
- Packet Processor
Each node generates its identity as:
Address = SHA-256(Public Key)
- Globally unique identity
- Cryptographically verifiable
- Resistant to spoofing
{
"version": 10,
"src": "hash_pubkey_sender",
"dst": "hash_pubkey_receiver",
"ttl": 5,
"type": "DATA",
"payload": "ENCRYPTED_DATA",
"signature": "SIGNATURE"
}- Node A connects to Node B
- Secure key exchange occurs
- A session key is established
- Payload is encrypted
- Packet is signed
- Packet is routed through intermediate nodes
- Destination verifies and decrypts
- Flood-based routing
- TTL-based loop prevention
- Path tracking (loop avoidance improvement)
- Adaptive routing
- Trust-based path selection
- Latency-aware routing
- AES-256-GCM (configurable)
- Ed25519 public/private key cryptography
- Packet-level signatures
Designed to integrate:
- CRYSTALS-Kyber (Key Exchange)
- CRYSTALS-Dilithium (Signature)
Adaptum IPv10 is designed to mitigate:
- Man-in-the-middle attacks
- Packet spoofing
- Traffic interception
- Future quantum decryption threats
- Private communication networks
- Secure peer-to-peer messaging
- Decentralized infrastructure
- Anti-censorship systems
- Research and experimental networking
- Initial version prioritizes security over speed
- Routing optimization planned in future versions
- Encryption overhead mitigated with symmetric keys
- Not natively supported by existing ISPs
- Requires overlay/tunneling
- Early-stage routing mechanism
- IPv10 prototype (basic routing)
- Secure communication layer
- Identity & signature system
- Post-quantum cryptography integration
- Advanced routing & optimization
| Feature | Traditional Internet | Adaptum IPv10 |
|---|---|---|
| Encryption by default | ❌ No | ✅ Yes |
| Decentralized identity | ❌ No | ✅ Yes |
| Quantum-resistant | ❌ No | ✅ Yes |
| Built-in security | ❌ No | ✅ Yes |
Adaptum IPv10 is not just an incremental improvement over existing protocols, but a fundamental redesign of how secure communication should work in a decentralized and quantum-aware future.
This commercial license is intended for organizations and enterprises that are unable or unwilling to comply with the terms of AGPLv3.
- Paid License – Required for organizations with more than 10 employees or concurrent users.
- No Source Code Disclosure – Modified code does not need to be publicly released.
- Closed Distribution Rights – Allowed for proprietary and closed-source environments.